Guest blog courtesy of Flare. This article has originally appeared on Cybercrime Diaries.
On February 20, 2025, the cybersecurity community received an unexpected stroke of luck as internal strife seemingly spread within the infamous Black Basta ransomware group. On that day, an unknown individual using the alias ExploitWhispers released a file on Telegram, allegedly containing the group’s internal chat logs[1]. As you may already know, the file is a JSON dataset comprising 196,045 messages from a Matrix/Element chat, primarily in Russian, spanning from September 18, 2023, to September 28, 2024[2].
While the true identity of the leaker and their actual motives remain unknown, ExploitWhispers accused Black Basta of crossing a red line by targeting Russian banks. A preliminary analysis suggests that most, if not all, of the leaked data appears legitimate. However, the possibility of data manipulation cannot be entirely ruled out.
Black Basta is a ransomware-as-a-service (RaaS) group that emerged in April 2022 and has since attacked over 500 organizations worldwide across various sectors, including healthcare, manufacturing, and utilities[3]. Notable victims include Ascension, Dish Network, Maple Leaf Foods, BT Group, and Rheinmetall. According to estimates published by The Record in November 2023, the group received over 100 million dollars in ransom payments to that date. However, since January 2025, no new victims have been reported, and the group’s leak site is presently down, suggesting that an internal conflict could have dislocated the group.
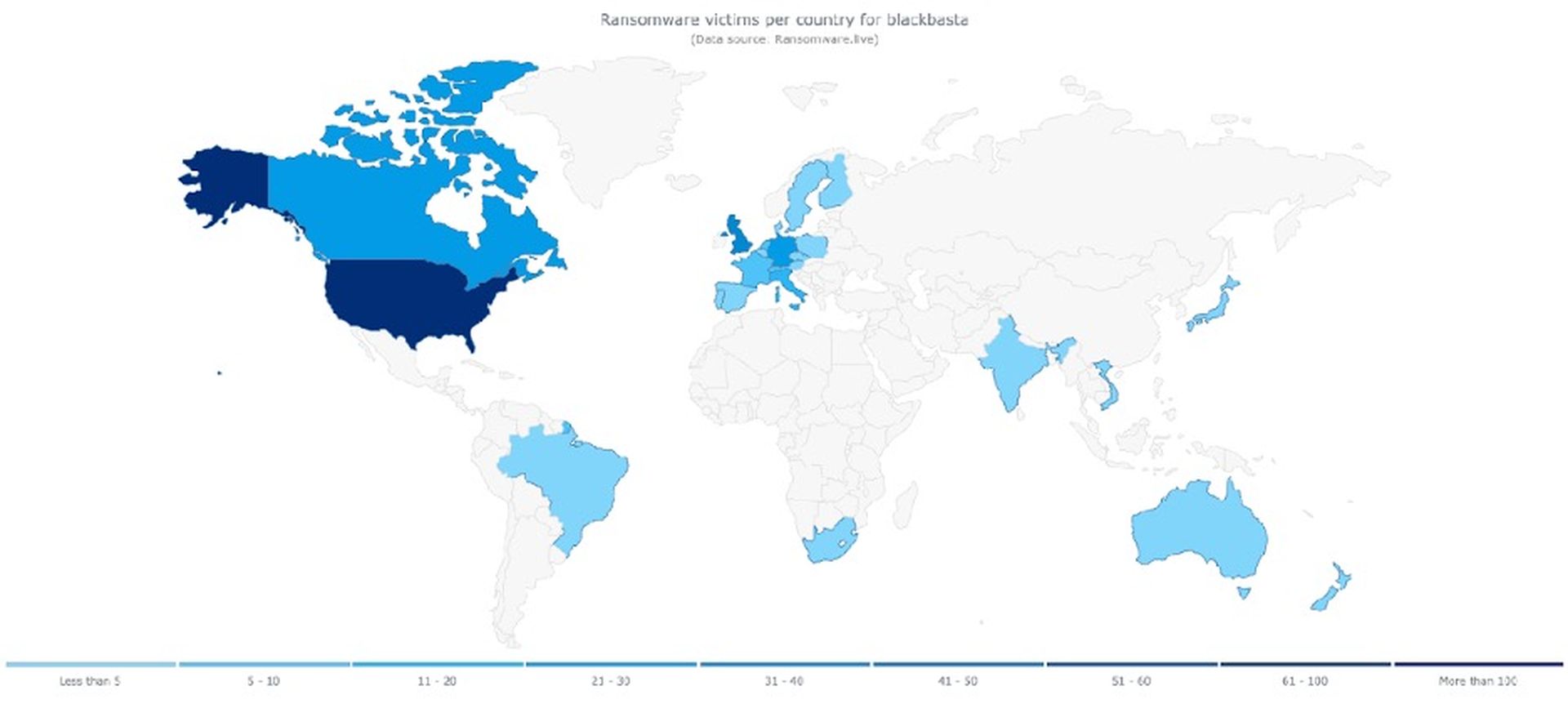
Figure 1. Source: Ransomware.live
Back in 2022, this RaaS was founded by Conti Team 3, also known as Tramp’s team, which remained in control of the group during the period covered by the leak. In the leaked chat, Tramp appears under the aliases gg and aa. An investigation by LeMagIT, supported by external sources, confirmed that the likely real identity of this threat actor is Oleg Nefedov, a Russian citizen originally from Yoshkar-Ola[4].
While extensive research has already been published, providing insights into who Nefedov is and which vulnerabilities the group exploited[5], this short blog will primarily focus on Black Basta’s internal organization. Additionally, I will offer a glimpse into how and where the group hosted and obfuscated its leak site and C2 servers. A big thanks to Tammy H and Estelle R for their help on this blog!
Here are some key observations from the leak and available information:
- Group members have several different specializations focusing on areas such as infrastructure management, initial access, malware and C2 obfuscation, development, and negotiations.
- A key distinction existed between threat actors who were employees of the group—working under Tramp’s direct and strict supervision in office settings—and more independent operatives, known as pentesters or affiliates, working online.
- These independent affiliates were often Tramp’s former associates from other illicit operations, such as Conti RaaS or banking trojans. They operate within their own teams, using distinct tools, methods, and internal hierarchies. This division sometimes leads to tensions between them and Black Basta’s core management.
A statistical analysis of the leaked data provided valuable insight into the group’s hierarchy. The most active user—by far—was the leader, Tramp, also known as “gg” (@usernamegg in the Figure 2 below). He was responsible for coordinating other members, developing new methods for obtaining initial access, participating in attacks, handling negotiations, and maintaining strict control over his employees. He enforced this control by personally visiting both offices where they operated.
Lapa is the second most active user; he can be described as a senior “pentester” who seemingly knew Tramp before joining the chat in September 2023. The majority of messages from this user were related to access to corporate networks of victims. Other active external pentesters such as “w” can also be noticed.
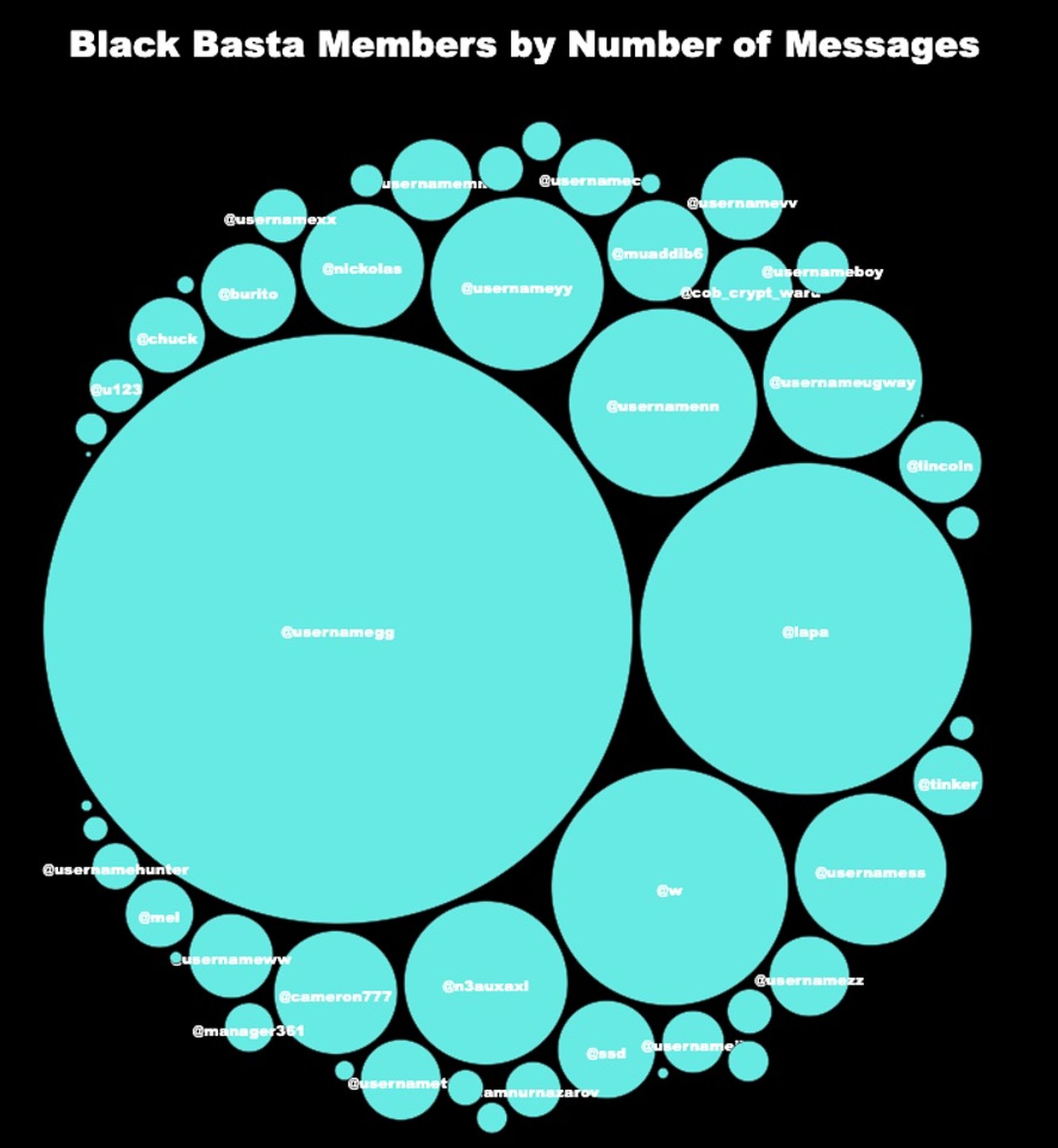
Figure 2. Source: Flare.io
The periods of activity and the nature of the messages themselves indicate that the group had specifically defined and organized vacation periods, like in January or June 2024, when almost all activity stopped.
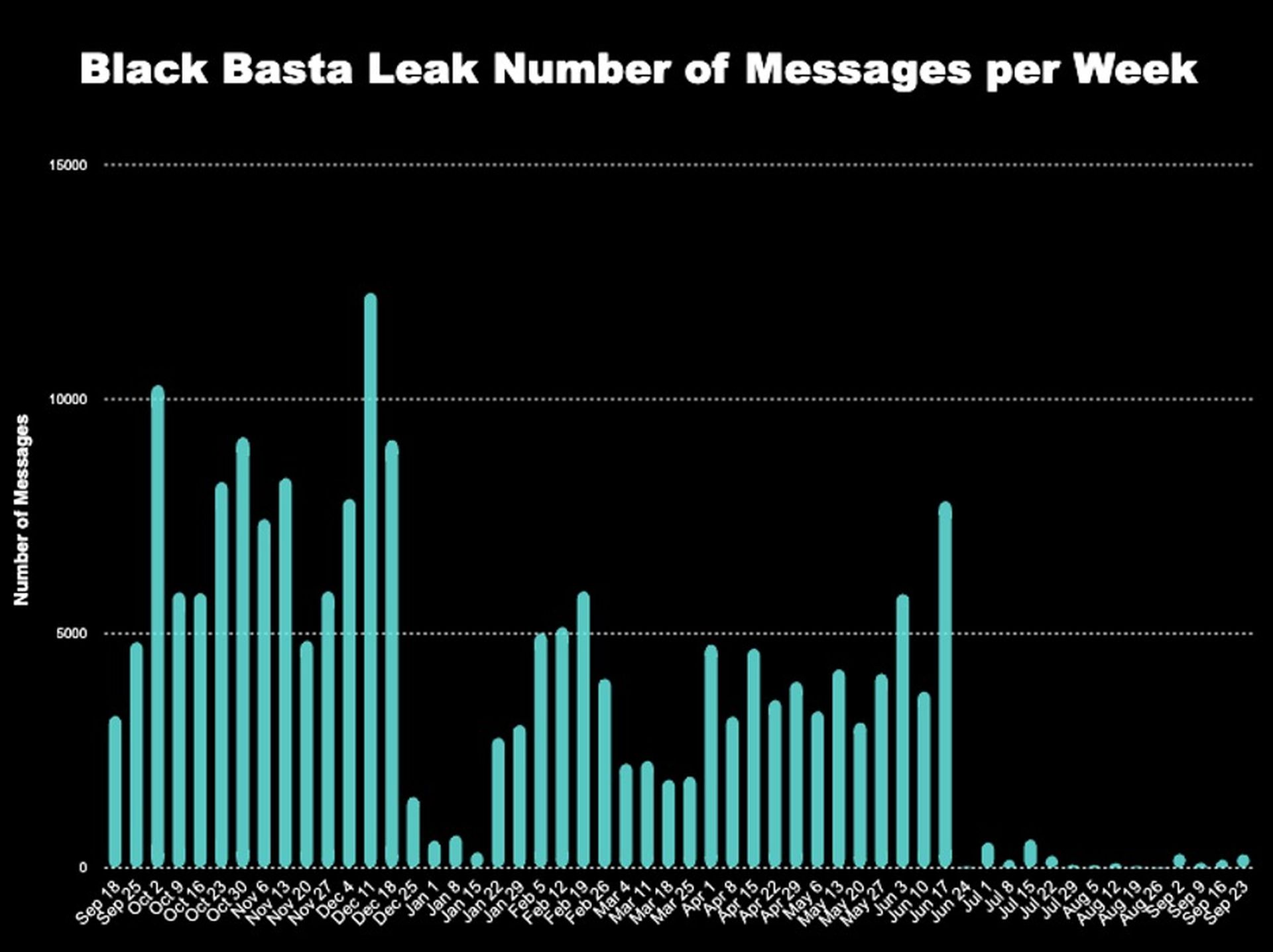
Figure 3. Source: Flare.io
Another notable observation was the distinct structure of the usernames present in the chat. Usernames composed of the word “username” followed by two letters—such as “gg” (aka Tramp), “ww”, “tt”, or “ss”—and hosted on the bestflowers247.online Matrix server appeared to belong to Black Basta’s core members (example: @usernamegg:bestflowers247.online). These threat actors were directly managed by Tramp, who also provided them with their Matrix accounts.
This structure clearly distinguished them from other members of the chat, who used their own Matrix servers, had different username formats, and operated more independently. These independent actors, which can be, in fact, considered affiliates, often referred to their own teams and other threat actors who were not part of the chat.
This differentiation is also highlighted in the graph below, where it can be seen that core members remained active for a much longer period than external ones. However, some noticeable discrepancies suggest that the data might be incomplete or that certain core members were simply dismissed in June 2024.
For instance, no disputes or conflicts were recorded for core members such as “ww”, “mm”, “zz”, or “cc”, yet the chat abruptly stopped in June 2024. This indicated the following possibilities: that the dataset is likely incomplete or that these members moved to another communication channel.
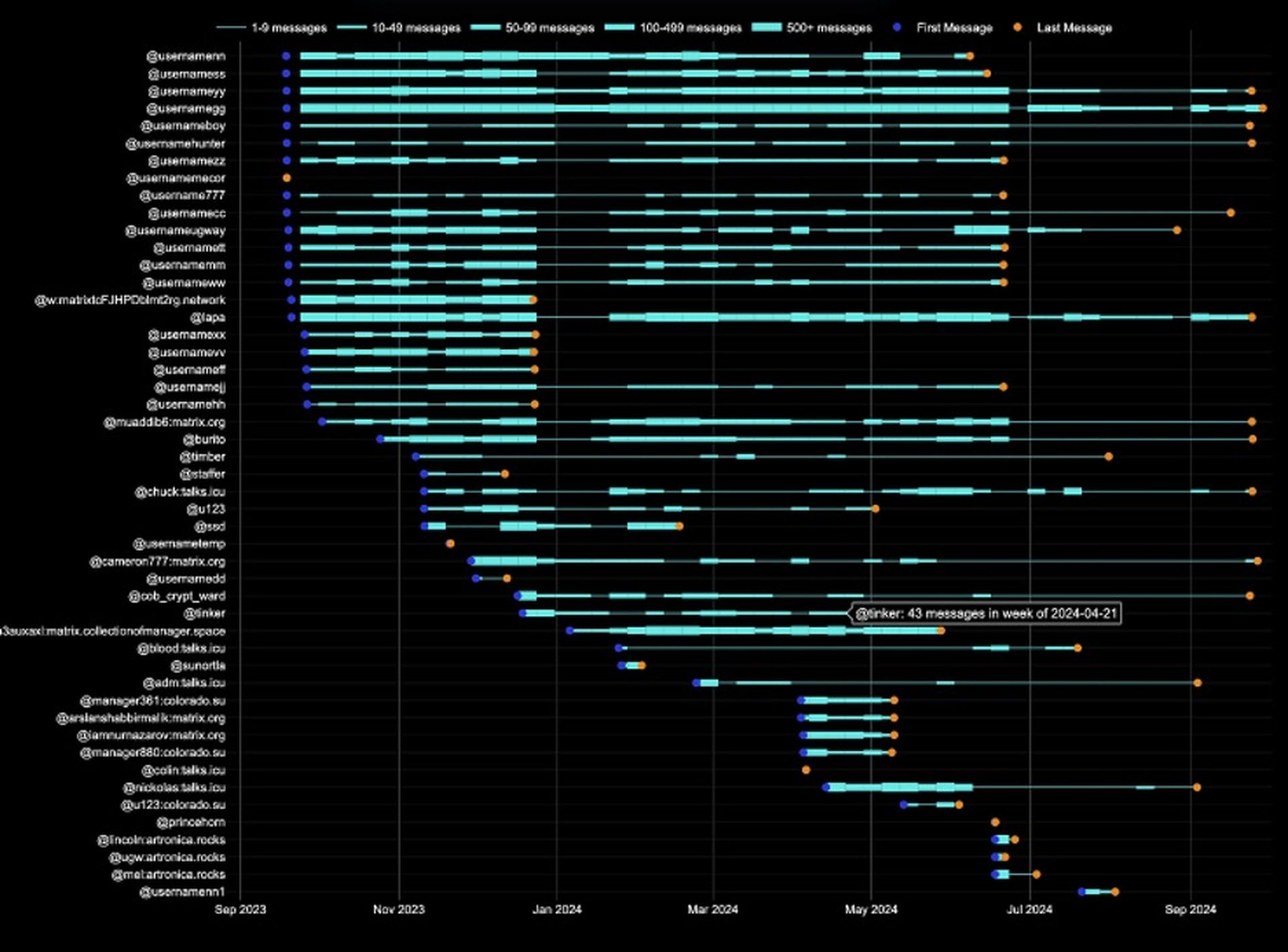
Figure 4. Source: Flare.io
By analyzing the various exchanges between members in the chat, I determined their main roles and specializations within Black Basta. As shown in the graph below—and accessible through the provided link—the group could be divided into the following specialties:
Black Basta’s internal organization.
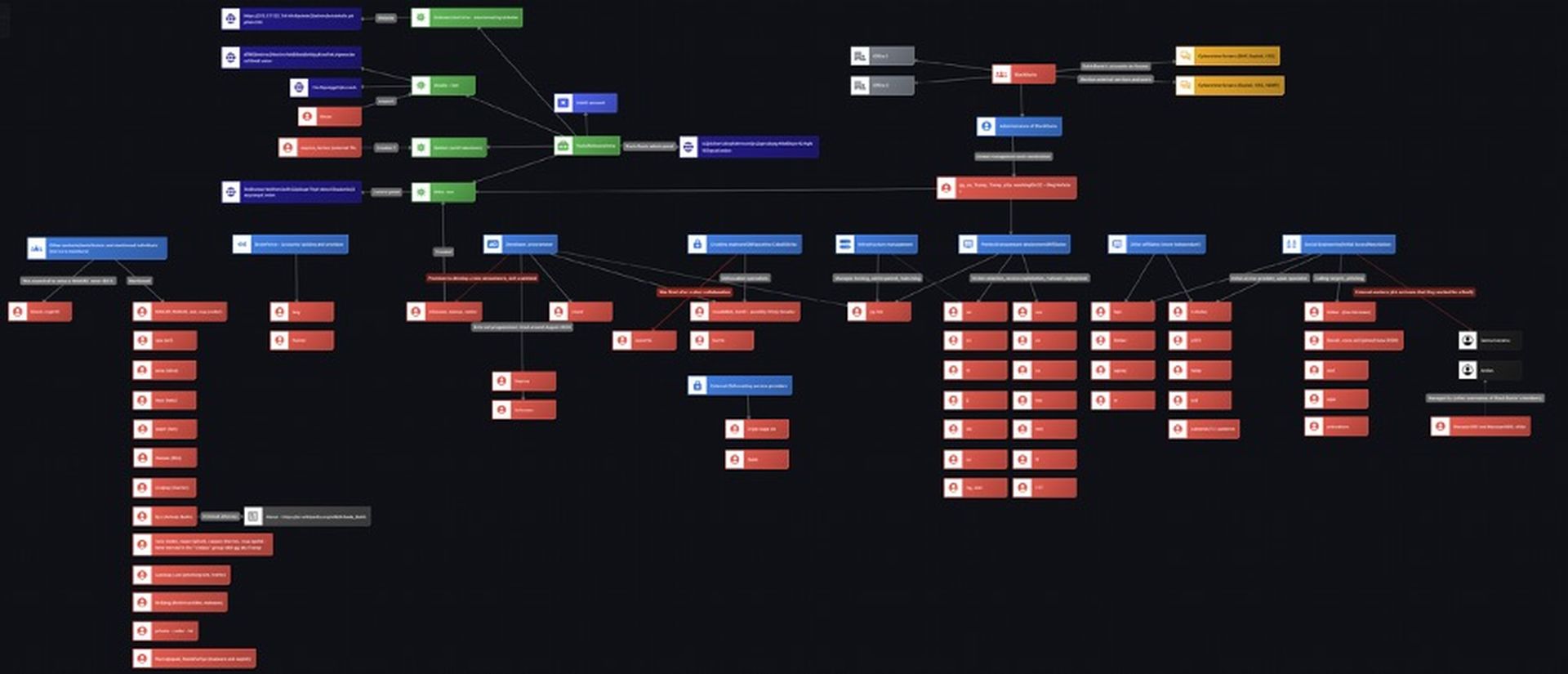
Figure 5. Source: Flare.io
II) Black Basta’s infrastructure - hosted in Germany and obfuscated.
Thanks to this preliminary work, which helped identify the main specialization of each threat actor active in the chat, it became easier to determine where to look for specific information, such as details about the group’s infrastructure.
According to the previous paragraphs and Figure 5, the threat actor yy, also known as bio, was responsible for Black Basta’s hosting, websites, and penetration testing servers.
As illustrated in Figure 6 below and in the graph available here, the group’s most critical servers were likely purchased from VPSKot, a company accepting cryptocurrency payments and reselling servers from legitimate hosting providers unaware of their real customers. One such provider was the German company Hetzner, where Black Basta hosted its Onion websites like the administrative panel, blog, and Element/Matrix chat service in September 2023.
Black Basta’s key servers in September 2023.
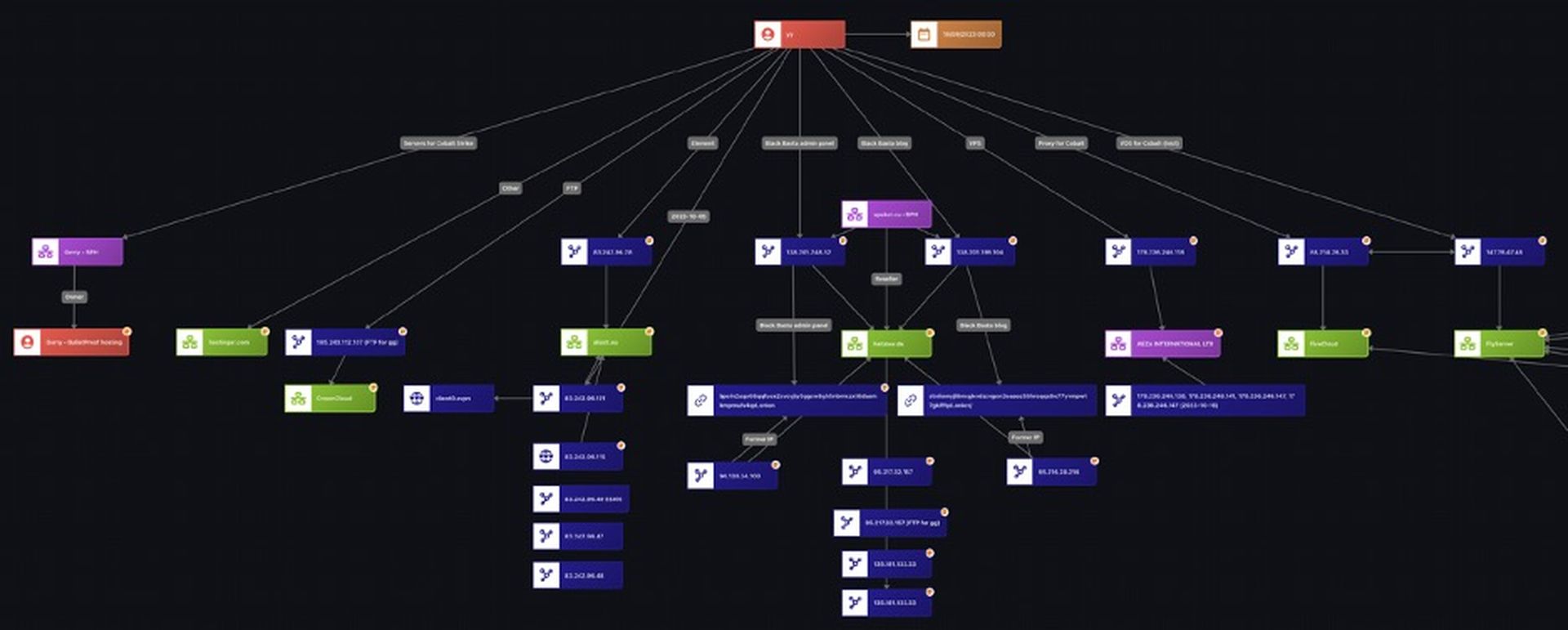
Figure 6. Source: Flare.io
The examination of yy’s messages from November 2023 also gives an interesting glimpse into how Black Basta deployed Cobalt Strike on servers and obfuscated them behind proxies. Cobalt Strike is a post-exploitation framework commonly used by red teams and cybercriminals to establish command and control, move laterally within networks, and execute malicious payloads.
The group seemingly used bulletproof hosting (BPH) but rather marginally, mainly preferring to acquire many servers from « grey » and offshore hosting companies to rotate their servers and obfuscate their sensitive infrastructure. One BPH that was still mentioned multiple times in the leak, referred to as « the Abkhaz hosting », was a service advertised by the threat actors « gerry », one of the most prominent illicit hosting presently active on Russian-language cybercrime forums.
Black Basta’s Cobalt Strike servers and proxies in November 2023.
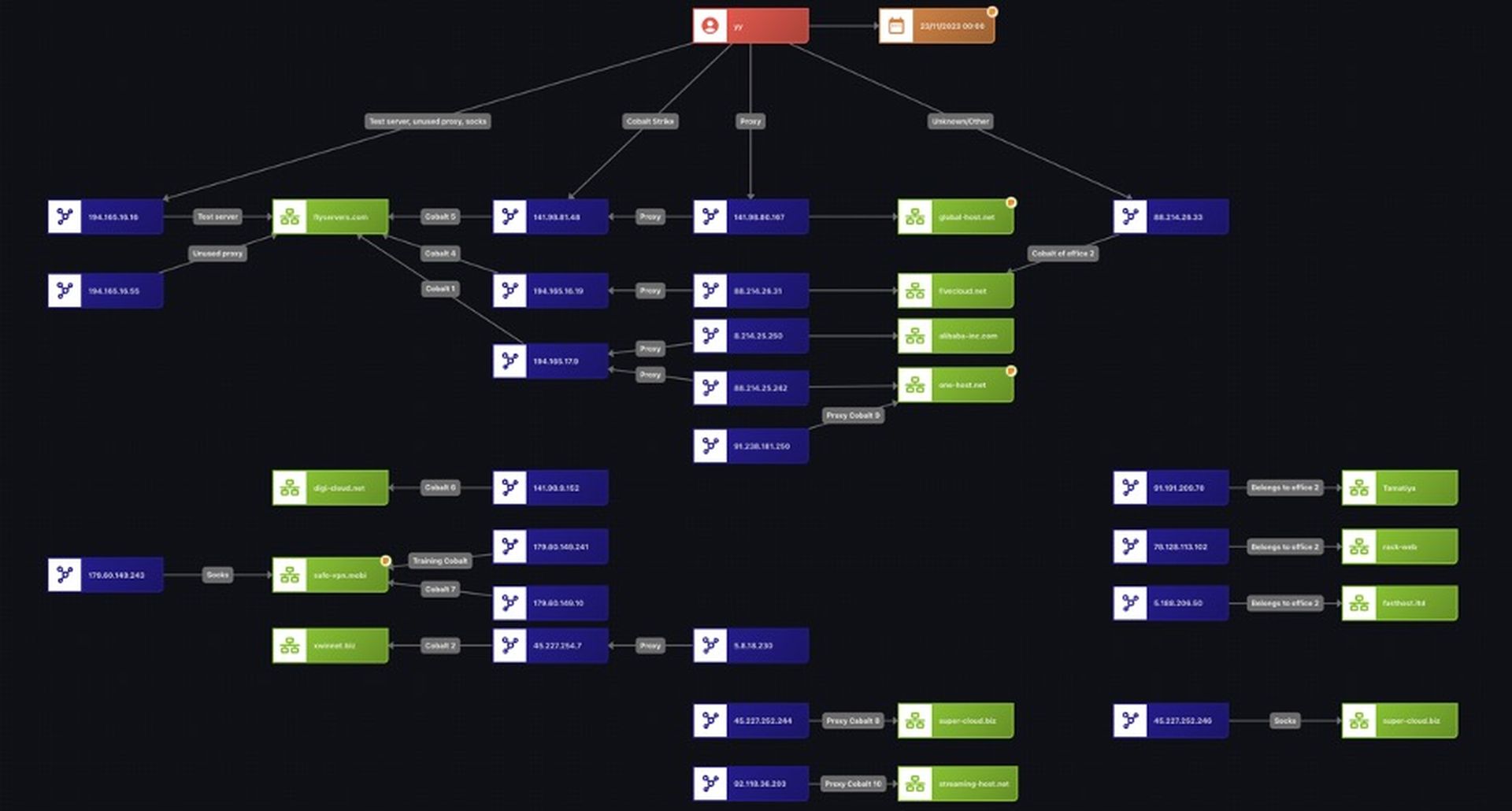
Figure 7. Source: Flare.io
Final thoughts: Black Basta leak - a treasure trove to explore.
This brief blog offers just a glimpse into the valuable information that can be extracted and analyzed from this leak. It contains numerous threat actor handles, illicit services from cybercrime forums, contact details, cryptocurrency addresses, and identified vulnerabilities. One particularly interesting investigative approach could be leveraging these indicators to track threat actor accounts across forums, potentially uncovering their real identities. For example I could identify several accounts on cybercrime forums of mentioned threat actors by a search in Flare.io with their TOX IDs.
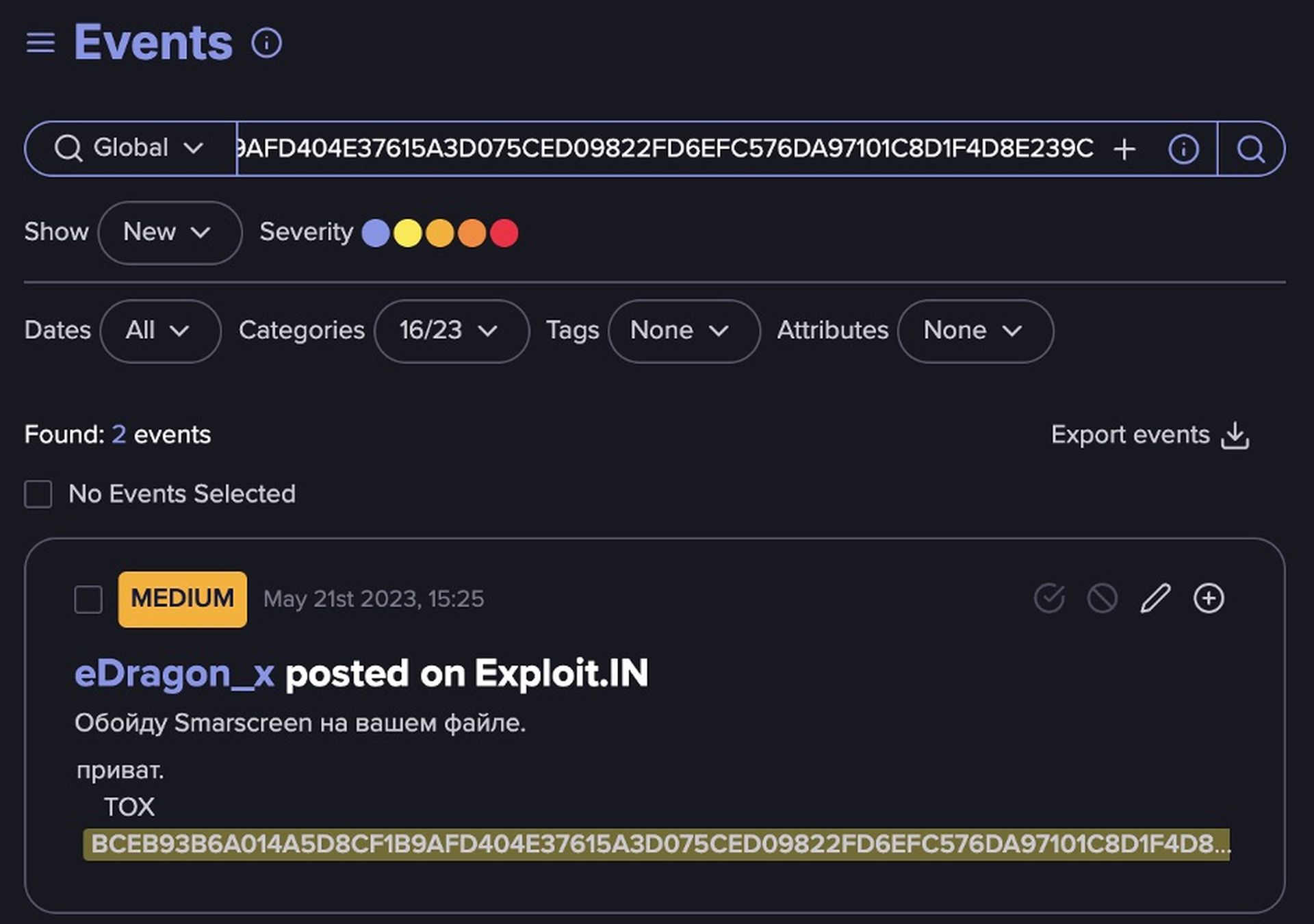
Figure 8. Source: Flare.io
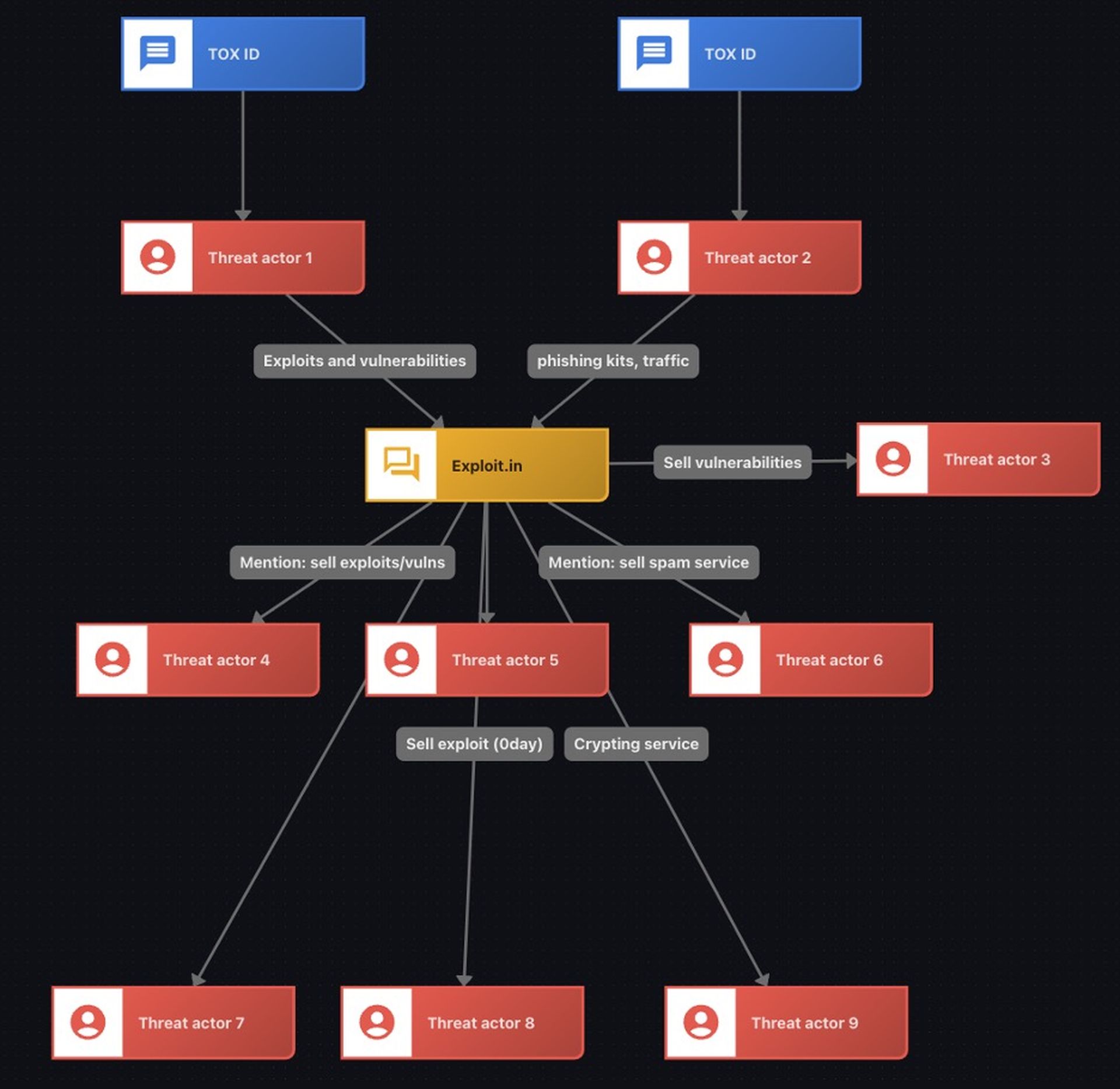
Figure 9. Examples of threat actors selling various services on Exploit that were mentioned in the leak.
Sources
[1] “Black Basta - Chat Viewer,” February 2025, https://ransomware-leaks.com/.
[2] Kevin Townsend, “Black Basta Leak Offers Glimpse Into Group’s Inner Workings,” SecurityWeek, March 3, 2025, https://www.securityweek.com/black-basta-leak-offers-glimpse-into-groups-inner-workings/.
[3] Ransomwarelive, "Black Basta - Ransomware.Live 👀,” March 5, 2025, https://www.ransomware.live.
[4] Valéry Rieß-Marchive, “Ransomware : de REvil à Black Basta, que sait-on de Tramp ?,” LeMagIT, March 1, 2025, https://www.lemagit.fr/actualites/366619807/Ransomware-de-REvil-a-Black-Basta-que-sait-on-de-Tramp.
[5] Patrick Garrity, “Exposing CVEs from Black Bastas’ Chats,” VulnCheck, February 24, 2025, https://vulncheck.com/blog/black-basta-chats.




